Having troubles with not activated Microsoft Windows or Microsoft Office product ? Solve your problems with most advanced kms pico activator provided with legit key management service ( KMS ). Download now and enjoy your activated Microsft product.
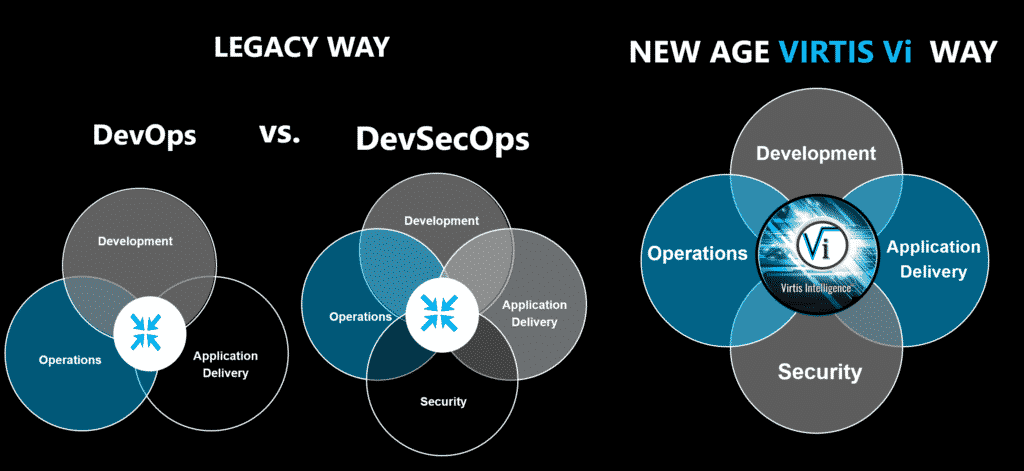
OUR DIFFERENTIATOR
We are filling a severe exposure gap in Web App & API Security.
WE DON'T TOUCH A SINGLE LINE OF SOURCE CODE
Our globally unique interception proxy transforms the application code on the fly removing the ability for vulnerabilities from being exploited, which is why we are safer and faster than anyone in the industry!
Keeping you 100% protected from ALL your known vulnerabilities.
Our streamlined automated platform is at an 80 to 1 ratio where it would take 80 people to our 1 automated service to achieve the same results which is why we are the most cost-effective solution in the industry.
Best of all, we provide an award-winning fully managed service with nothing for you to manage on your end! Guaranteeing we will keep you 100% protected against all of your known vulnerabilities.

48% of all breaches come through WEB APPS
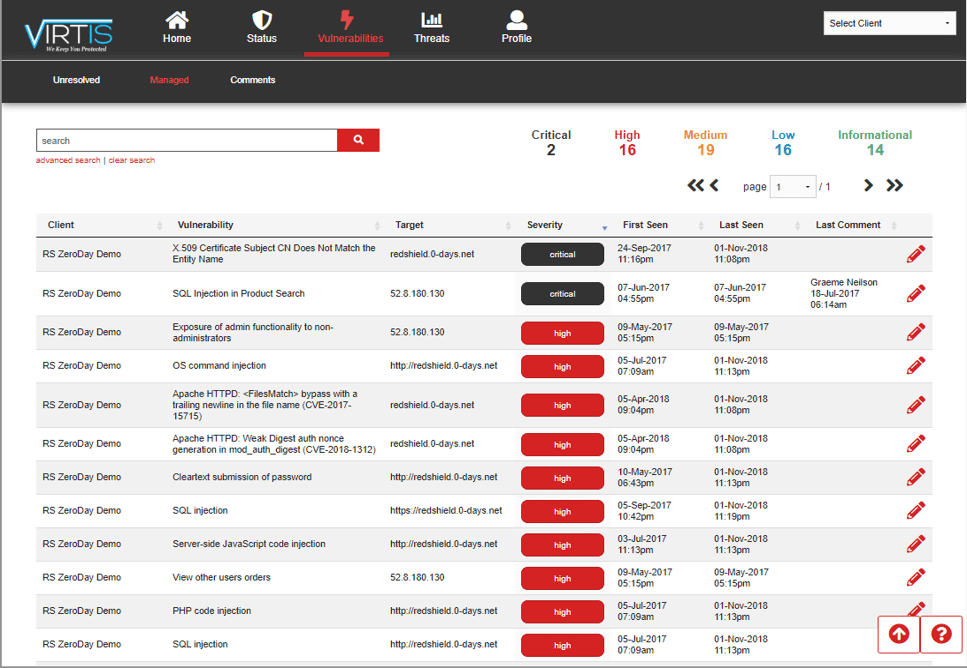
Web apps, on average, have 12-20 vulnerabilities "weaknesses" that make it easy for hackers to breach.
Currently, the only way to fix vulnerabilities is for developers to rewrite application code; it's very time consuming and expensive. Developers, on average, take 4-6 months to rewrite application code.
Why be exposed waiting months for developers to rewrite application code?
Are you willing to take that gamble?
WE IMMEDIATELY PROTECT YOUR ENTIRE DIGITAL NETWORK PERIMETER.
According to a 2018 Verizon Data Breach Investigations Report, web applications were the biggest target for data breaches (again), and high for incidents. WhiteHat agrees that the state of application security has progressively deteriorated year-over-year.
~ WhiteHat Security©2019
Cybersecurity doesn’t have to be complicated, we are here to help.
Whether your focus is complex web applications, platforms or frameworks in Azure, AWS, GCP or on-premise, we have the expertise to protect your unique needs.
Web applications are only becoming more relevant. Millions of organizations and people rely on web apps to make their work environments more efficient and handle their most sensitive information. With their growing demand for web apps, there comes more and more unforeseen security flaws and simple human error. This risk increases as web applications become more interconnected through the integration of APIs.
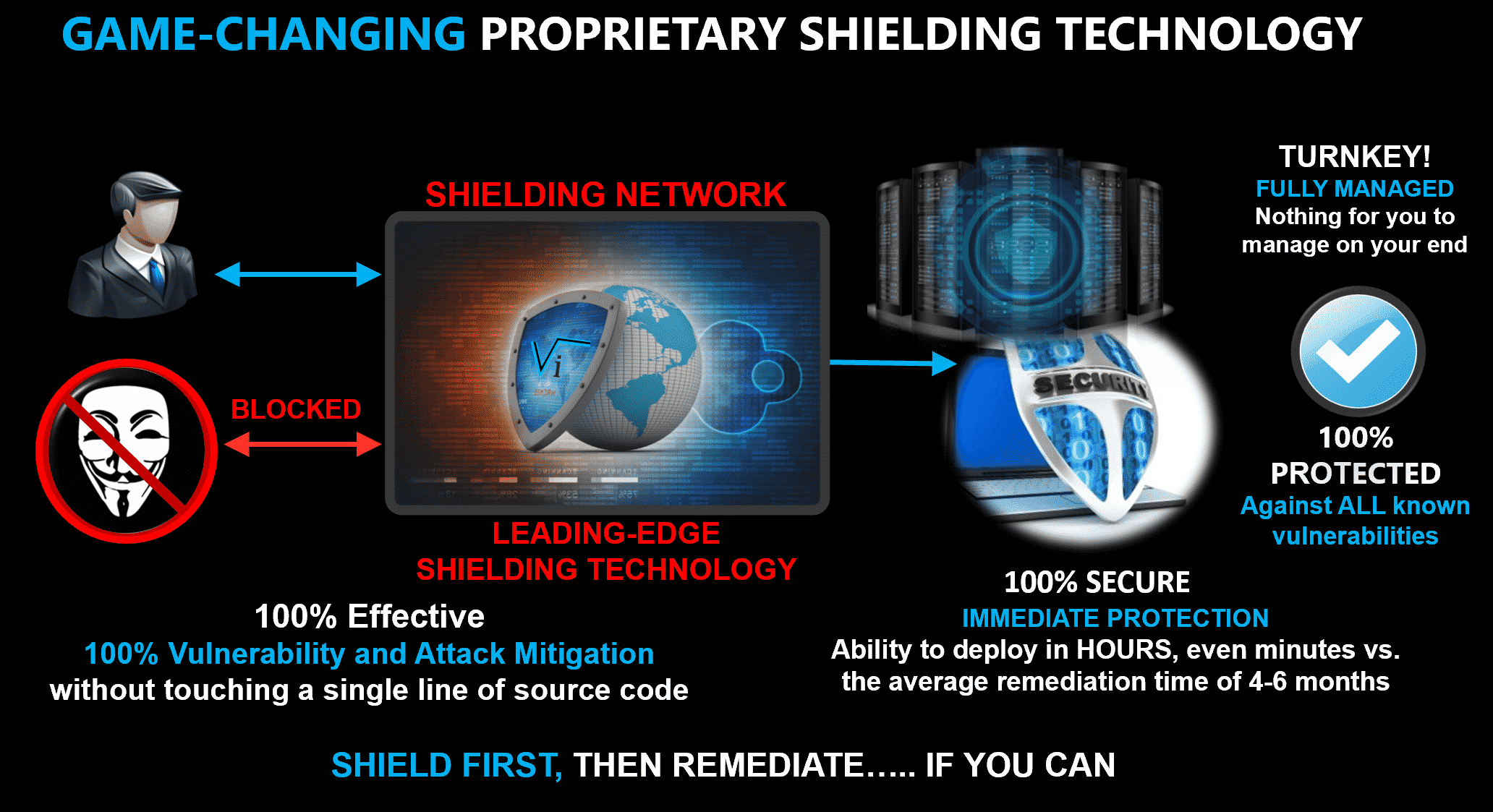
GAME-CHANGING SHIELDING TECHNOLOGY
Currently, the only way to fix vulnerabilities is for developers to rewrite application code; it's very time consuming and expensive.
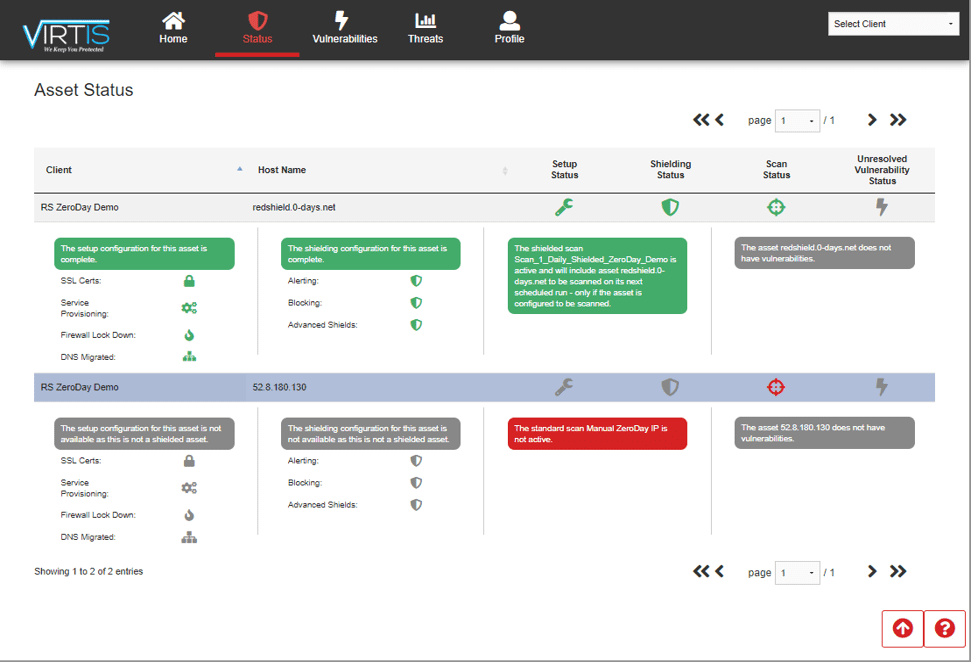
Unlike current remediation time averaging 4-6 months to rewrite application code, VIRTIS protects immediately upon deployment (in hours, even minutes). Our shielding technology, an impenetrable shielding network envelops your entire digital network perimeter keeping you safe from hackers and data breach.
We don’t touch a single line of source code. Our interception proxy transforms application code on the fly, nullifying exploitability.
Best of all, it’s a fully managed service with nothing for you to manage on your end!
NOT TO BE CONFUSED WITH A WAF
Not to be confused with a Web Application Firewall (WAF). We pick up where WAF’s fall short. WAFs cannot fix business logic flaws because they cannot maintain application state. We can. A well-managed WAF needs a skilled engineer on-site and at best can only protect up to 30% still leaving you 70% exposed. We protect what a WAF can in our baseline policy with our fully managed service.
Award-Winning 24/7 Fully Managed SHIELDING Service
We advocate for code remediation when possible. However, that is not always achievable. With 50+ new vulnerabilities coming out every day, it is almost impossible to keep up.
Long gone are the days of waiting months for developers to rewrite application code.
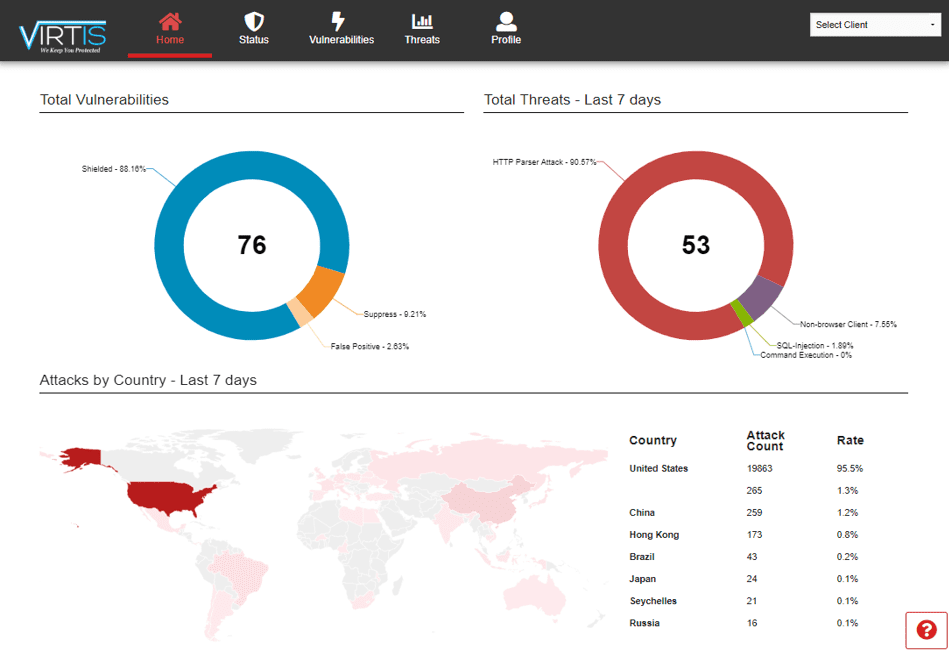
Our 24/7 Fully Managed Service keeps you protected with nothing for you to manage on your end! We provide real-time application protection reporting along with customer portal access to our processes and world-class expertise.
99% PROTECTED IS STILL 100% EXPLOITABLE.
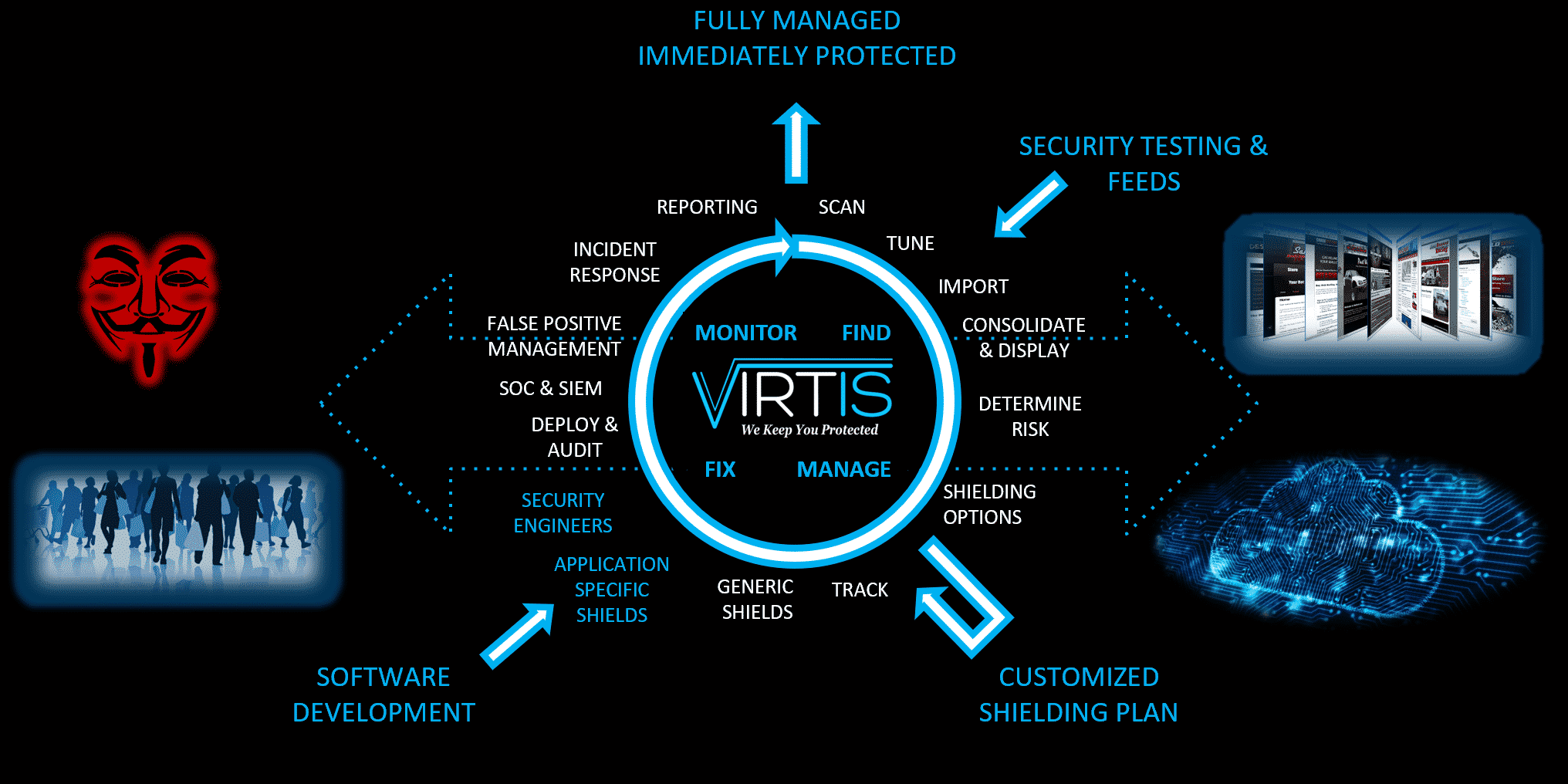
Security Operations Center
We are 10-100 times safer, faster and less expensive than doing it yourself, rewriting the source code, or replacing software.
Modernizing Application Security